Why Us
Cybersecurity & Data Protection: Safeguarding Your Digital Ecosystem
Our Cybersecurity & Data Protection services at ZS Global are designed to protect organizations from evolving cyber threats while ensuring data integrity, confidentiality, and compliance. By implementing advanced security frameworks, proactive monitoring, and risk management strategies, we help businesses operate securely in an increasingly digital environment.
We take a holistic approach to cybersecurity that goes beyond basic protection. Our services focus on prevention, detection, and response, ensuring your systems, applications, and data remain resilient against threats. With ZS Global as your security partner, your organization gains confidence, stability, and long-term digital trust.
Comprehensive Threat Assessment and Risk Management
We conduct in-depth security assessments to identify vulnerabilities across infrastructure, applications, and data environments. This proactive approach enables early risk mitigation and strengthens your overall security posture.
-
Data Protection and Privacy Assurance
Our data protection strategies focus on securing sensitive information through encryption, access controls, and data governance practices. We help organizations protect critical data while maintaining compliance with industry regulations and privacy standards.
-
Proactive Security Monitoring and Incident Response
Proactive Security Monitoring and Incident Response ZS Global provides continuous monitoring and rapid incident response to detect and address potential threats in real time. This ensures minimal disruption and faster recovery in the event of a security incident.
-
Secure Infrastructure and Network Protection
We implement robust security measures across networks, cloud environments, and on-premise systems. Our approach ensures secure connectivity, controlled access, and protection against unauthorized activities.
-
Application and Endpoint Security
Our cybersecurity services include securing applications and endpoints through vulnerability management, patching, and access control. This reduces exposure to threats and enhances system reliability.
-
Compliance and Regulatory Alignment
We help organizations meet regulatory requirements and industry standards by implementing compliance-driven security controls. Our structured approach ensures audit readiness and risk reduction.
-
Business Continuity and Resilience Planning
Our cybersecurity strategy includes disaster recovery and business continuity planning to ensure operational resilience. This allows your organization to maintain continuity even during security disruptions.
Our Process
Structured Security Framework for Reliable Protection
We begin with a comprehensive evaluation of your existing security posture to identify gaps, risks, and improvement opportunities.
Based on assessment findings, we design a tailored cybersecurity strategy aligned with your business objectives and risk profile.
Our teams deploy security tools, policies, and controls across systems, networks, and data environments to establish strong protection layers.
We implement monitoring solutions that provide real-time visibility into potential threats, enabling proactive response and mitigation.
In the event of a security incident, our response framework ensures rapid containment, investigation, and recovery to minimize impact.
We provide regular reporting and validation to ensure ongoing compliance with security standards and regulatory requirements.
Our cybersecurity services evolve with emerging threats, ensuring continuous improvement and long-term protection.
Our Initiative
Transformative Business Outcomes
- Proactive Cyber Threat Prevention
- Data Privacy and Regulatory Compliance
- Secure Infrastructure and Application Protection
- Real-Time Monitoring and Incident Response
- Business Continuity and Disaster Recovery Planning
- Risk Reduction Through Structured Security Controls
- Long-Term Digital Trust and Resilience

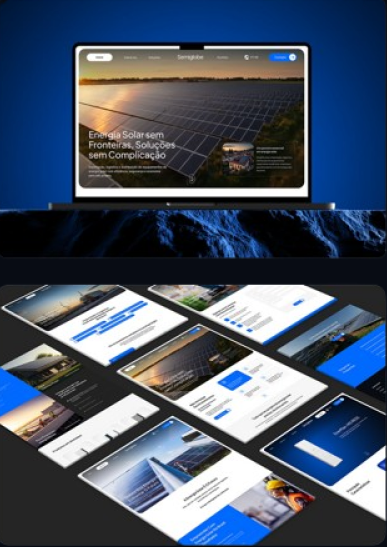
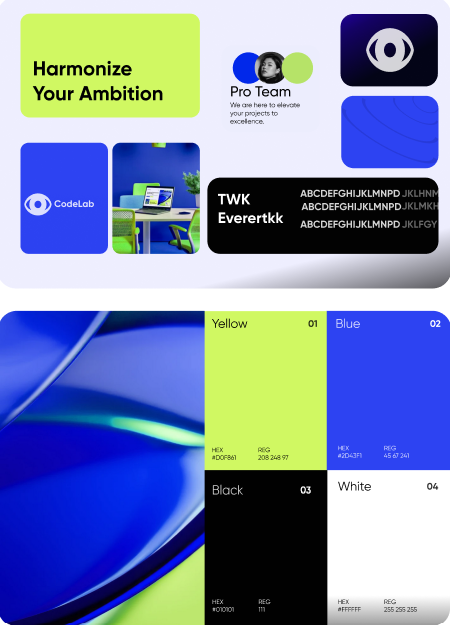
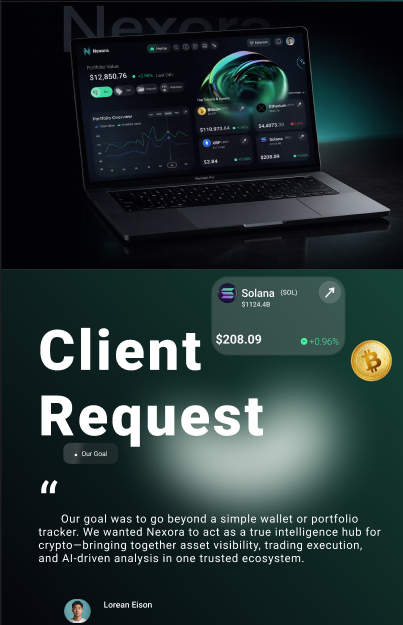
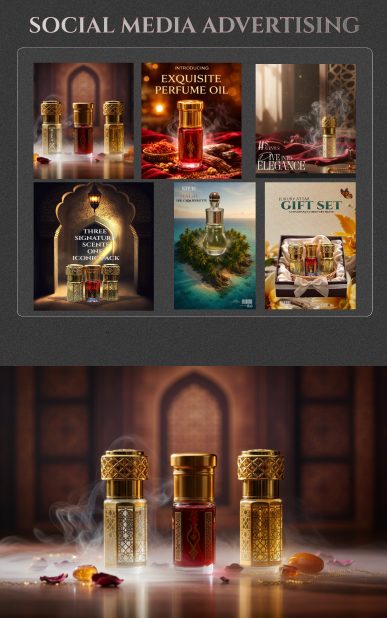
Our Works
FAQ
Cybersecurity & Data Protection: Frequently Asked Questions (FAQs)
What does Cybersecurity & Data Protection include?
How can cybersecurity services benefit my business?
Do you provide cloud and on-premise security?
How do you handle security incidents?
Can you help with compliance requirements?
How do you ensure ongoing protection?
How do I get started with Cybersecurity & Data Protection services?
Partnering with ZS Global for Cybersecurity & Data Protection
ZS Global delivers comprehensive cybersecurity and data protection solutions that help organizations operate securely and confidently. Our expertise, proactive approach, and commitment to resilience ensure that your digital assets remain protected in a rapidly evolving threat landscape.
Contact Us
How Can
We Help You?
We Help You?
-
You can also write us on our e-mail
corporate.communications@zs-global.us