Why Us
Transforming your vulnerabilities into strengths with comprehensive cybersecurity protection
ZS Global is aware that the digital realm is in constant flux, bringing new challenges and threats to businesses of every size. Our extensive cybersecurity solutions are designed to defend your business against various cyber threats, from data breaches to malware attacks. Our team of experts leverages the latest technologies and industry best practices to create a robust security framework that protects your essential assets. By conducting thorough risk assessments and implementing tailored security measures, we help you identify vulnerabilities and fortify your defences.
With ZS Global, you can trust that your sensitive information is secure, allowing you to focus on what matters most—growing your business with peace of mind.
Ensuring Business Success Through Effective Cybersecurity Solutions
- Navigating Growth with Strong Cybersecurity
Business growth brings evolving cybersecurity requirements. We understand the need for flexible security solutions and provide scalable network security services incorporating advanced encryption techniques and proactive threat detection. These services ensure that your expanding infrastructure remains protected against potential cyber threats.
- Anticipating Future Threats in a Dynamic Environment
The threat landscape is becoming more complex as artificial intelligence and emerging technologies transform various industries. We offer comprehensive cloud security measures and sophisticated information security protocols powered by AI-driven threat intelligence. This proactive approach helps safeguard businesses against contemporary cyber challenges, keeping them ahead of potential threats.
- Integrating Modern Security with Legacy Systems
Many businesses still rely on legacy systems that may have security vulnerabilities. We specialize in enhancing these older systems by integrating modern security practices. Our approach strengthens your existing infrastructure while minimizing the risks associated with outdated technology.
- Prioritizing Data Privacy and Protection
Data privacy is critical. We implement robust strategies focused on solid encryption and effective identity and access management (IAM). Our solutions protect sensitive information from unauthorized access and ensure compliance with data protection regulations, fostering trust among your customers.
- Maintaining Compliance with Regulatory Requirements
Compliance with industry regulations is vital for your business’s integrity and reputation. Our cybersecurity experts conduct thorough cyber risk assessments and regular security audits to help your business meet applicable legal standards. We also develop governance policies aligned with best security practices to ensure your operations remain legally sound and secure.
- Proactive Security through Continuous Monitoring
The cyber threat landscape constantly evolves, and your defences must adapt. We provide ongoing monitoring services and managed detection and response (MDR). Our team conducts regular security assessments and penetration testing to ensure that your defences are proactive and responsive, ready to tackle new threats as they arise.
- Enhancing Employee Awareness and Engagement
Human factors play a significant role in cybersecurity vulnerabilities. We offer tailored training programs to enhance employee awareness of cybersecurity threats. By equipping your team with the knowledge to identify and respond to potential risks, we help foster a robust security culture within your business.
- Custom Security Strategies for Unique Industries
Different sectors face distinct cybersecurity challenges. We customize our security solutions to meet the specific needs of your industry. This tailored approach ensures that your business can effectively manage its unique vulnerabilities while remaining compliant with regulatory standards and best practices.
Our Process
Cybersecurity Assurance: Building a Resilient Defense Strategy
Our process begins by identifying and understanding vulnerabilities within your organization. Through a thorough cyber risk analysis, we detect potential threats, evaluate weaknesses, and estimate the potential impact of security breaches, equipping your business to stay one step ahead.
With risk assessment insights, we craft customized security policies that set robust standards for data handling, access management, compliance, and governance. These policies ensure that every aspect of your digital framework remains secure and meets industry regulations.
We deploy cutting-edge security protocols, including network defence systems, firewalls, encryption, and intrusion detection tools, creating a comprehensive shield against cyber threats. Our multi-layered approach ensures maximum protection across all business touchpoints.
Human error is a critical vulnerability in cybersecurity. Our training programs equip your team with essential security skills, enabling them to recognize suspicious activities, follow safe data practices, and help prevent potential threats.
Continuous, real-time monitoring is essential for fast threat detection. Our monitoring services, which include traffic analysis, vulnerability scanning, and managed detection and response (MDR), identify potential risks swiftly and allow rapid response to threats.
A swift, coordinated response to security incidents is crucial. We work with you to establish a customized incident response plan that addresses threat containment, communication protocols, and recovery strategies, ensuring a structured and effective resolution.
Cyber threats evolve, and so should your defences. We provide regular system updates and timely patch management to address emerging vulnerabilities, ensuring your infrastructure remains resilient and up-to-date.
Staying compliant with industry standards is paramount. Our governance services include routine audits and compliance checks, allowing you to maintain regulatory and security integrity while mitigating potential risks.
In an ever-evolving cyber landscape, ongoing evaluation is crucial in maintaining resilience. We partner with your team to reassess strategies regularly, adopt advanced technologies, and improve defences against new and emerging threats.
An effective cybersecurity strategy includes planning for the unexpected. We provide comprehensive data backup and disaster recovery solutions, ensuring your business can recover quickly and minimize downtime in a significant cyber event.
Our Initiative
Protect Your Digital Assets with Proven Security Strategies
- Accelerated Revenue Growth & Market Position
- Enhanced Operational Efficiency & Service Delivery
- Strengthened Customer Loyalty & Brand Reputation
- Scalable Solutions for Long-Term Business Growth
- Data-Driven Insights for Informed Decision Making

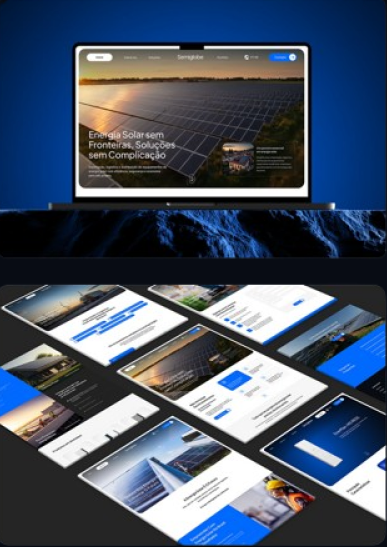
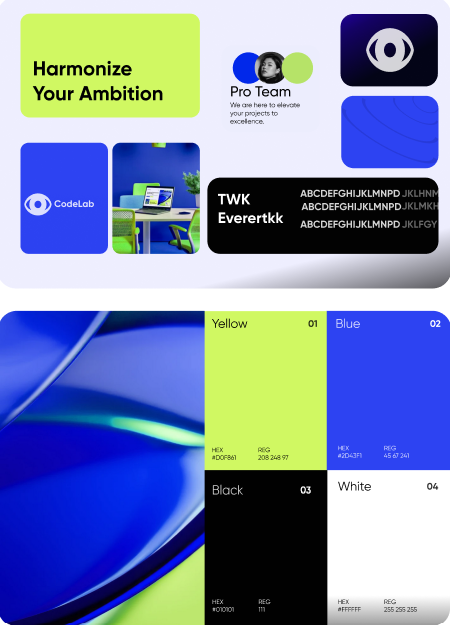
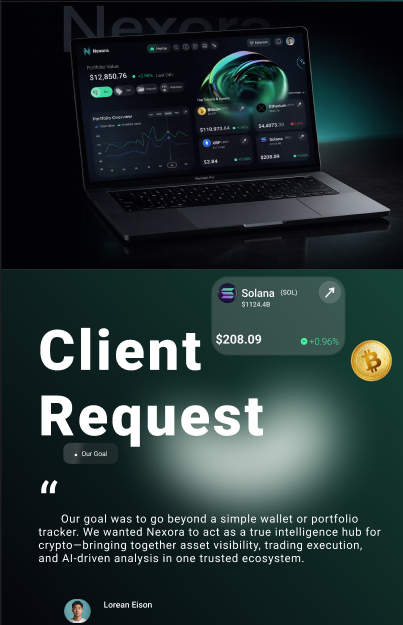
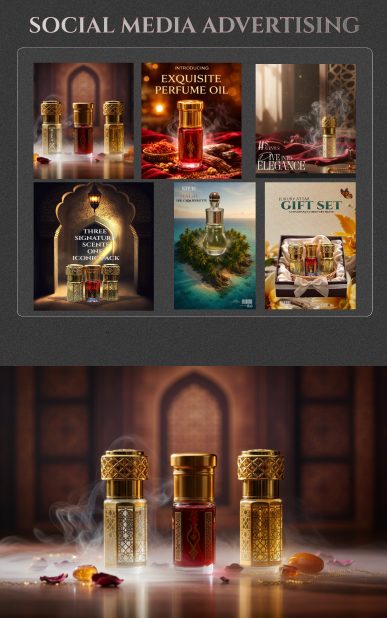
Our Works
FAQ
Cybersecurity: Frequently Asked Questions (FAQs)
What cybersecurity services does ZS Global offer?
How does ZS Global help prevent data breaches?
Why is employee cybersecurity training important?
What is the purpose of continuous monitoring in cybersecurity?
How does ZS Global ensure compliance with industry regulations?
What is an incident response plan, and why do I need one?
How does ZS Global address the security needs of different industries?
Why is proactive cybersecurity critical for my business?
How does ZS Global handle data backup and disaster recovery?
What should I expect from a cyber risk assessment with ZS Global?
Resilient Cybersecurity: Your Partner in a Secure Digital Future
Cybersecurity is about more than defence—it’s about trust and stability as your business grows. ZS Global crafts a dynamic, trusted security ecosystem that scales with you, reinforced by regular threat intelligence updates and adaptive defences. With ZS Global, you’ll have a lasting cybersecurity foundation that strengthens and supports your journey into the future. Secure your peace of mind with ZS Global today.
Contact Us
How Can
We Help You?
We Help You?
-
You can also write us on our e-mail
corporate.communications@zs-global.us